We are happy to announce that we have added a new staff member to our growing team! Ed Zuidema joined PCM in March and will be working as a Primary Technician with clients. Ed has over 25 years of IT experience, including working for a university for a large part of his career.
PCM’s newest Technical Consultant
Season’s Greetings from PCM
PCM adds another Help Desk team member

Eddie Jakupovic joined our team in September to increase the number of Help Desk technicians we have on staff. Eddie comes to us with a fair bit of industry experience, most recently working for a family business as an IT Technical Specialist. He also holds a Mohawk College Computer Systems Technician diploma which is a program a number of us have gone through.
PCM adds another Help Desk team member

Roopa Johny joined our team in September to increase the number of Help Desk technicians we have on staff. A few years ago, she graduated from Georgian College from their Computer System Technician/Networking program. After that Roopa gained a couple years of experience as a help desk technician at a larger accounting firm.
Introducing Salvator As A New Team Member
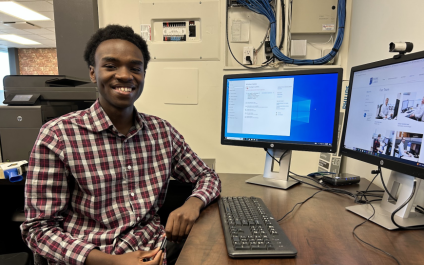
Salvator Muhire has been with us a few months as a Help Desk Technician. Salvator comes to us through the Mohawk College co-op program where he is completing the Computer Systems Technology - Network Engineering & Security Analyst program. Salvator is working with us for an 8-month term, after which he will return to school to complete his final year.
How to increase the life span of your business computer and hardware

If you rely heavily on computers for routine tasks in daily operations, making sure they keep running as smoothly and efficiently as possible is essential. When done right, maintaining your PCs, as well as other hardware, will ensure more efficient workflows and fewer annoying IT hiccups along the way.
Season’s Greetings from PCM

As we approach the end of another year, we wanted to take a moment and send season’s greetings from all of us. Wishing you and your loved ones a Merry Christmas and all the best in the coming year.
Ed & Henrietta VanderLaan, Adrian VanderLaan and staff:
Maurice Brink, Gary Halbig, Joel Harsevoort, Tanya Jerome, Mark Kottelenberg, Mickael Moco, Tina Morris, Scott Ritchie, Mike Tigchelaar, Joshua Shurvell, David Vanden Ende, Alvar Vandenbeukel, and Dave VanderMeulen.
Introducing Josh as a new team member

Joshua Shurvell has recently joined our company as a Help Desk Technician. Josh comes to us through the Mohawk College co-op program where he is completing the Computer Systems Technology – Network Engineering & Security Analyst program. Josh is working with us for the fall term, after which he will return to school to complete his final year.
Introducing Tanya as a new team member

We are happy to introduce Tanya Jerome who recently joined our company as an Office Administrator. This is a new position for us as we grow and realized that we needed assistance in several areas in the office. She’s the friendly person you meet when contacting our office and looks after procuring all the hardware and software needed for our clients along with many other related tasks in the office.




